Исходя из соображений безопасности сообщества - автор: WhoTookMyCrypto.com
2017-й был замечательным годом для индустрии криптовалют, так как их быстрый рост цены привлек пристальное внимание средств массовой информации. Неудивительно, что это вызвало огромный интерес как у широкой публики, так и у киберпреступников. Относительная анонимность криптовалюты сделала ее фаворитом для тех, кто использует ее для того, чтобы обойти традиционные банковские системы и избежать финансового надзора со стороны регулирующих органов.
Учитывая что люди проводят большую часть своего времени пользуясь смартфоном в отличии от ПК, неудивительно что киберпреступники сконцентрировали свое внимание именно на нем. Дальнейшая информация показывает то, как мошенники нацелены на смартфоны пользователей криптовалюты, а также несколько шагов, которые можно предпринять, чтобы защитить себя.
Поддельные приложения
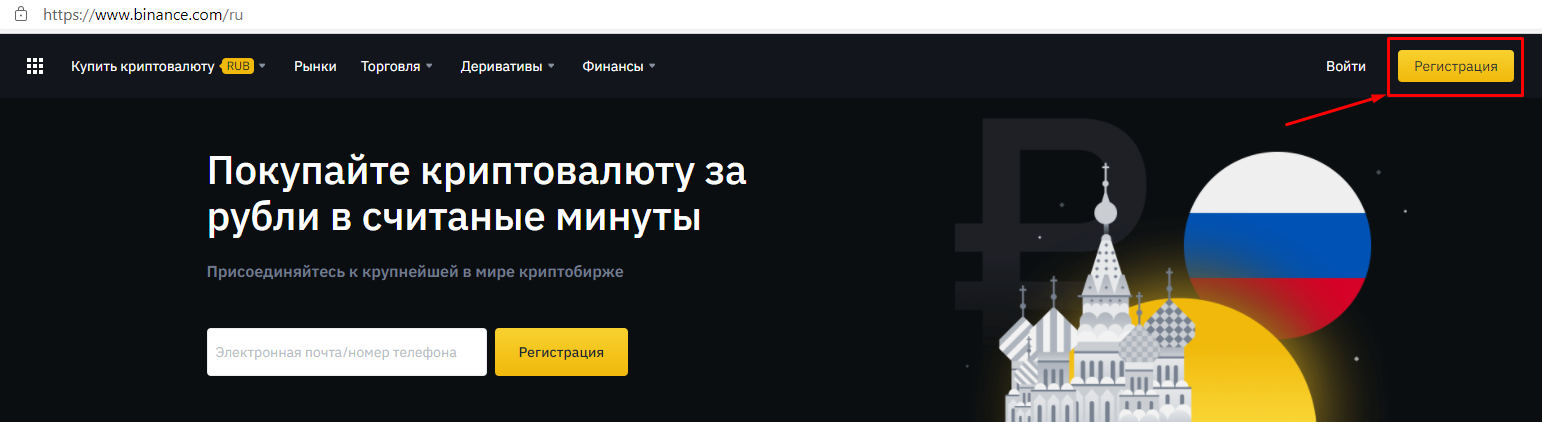
Криптовалютные биржи
Наиболее известным примером подобного программного обеспечения для смартфона является мобильное приложение для доступа к аккаунту в Poloniex. До запуска официальной версии в июле 2018 года, Google Play уже насчитывал несколько поддельных приложений, которые были намеренно разработаны, чтобы их нельзя было отличить от оригинала. Многие пользователи, которые скачали и установили эти программы, скомпрометировали свои учетные данные для входа в биржу, а их криптовалюта была украдена. Некоторые приложения пошли дальше и начали запрашивать Gmail аккаунт. Важно отметить тот факт, что все учетные записи жертв были без наличия двухфакторной аутентификации (2FA).
Вы можете обеспечить свою безопасность с помощью следующих действий:
-
Посетите официальный веб-сайт биржи, чтобы убедиться в том, что у них действительно существует мобильное приложение. Если это так, используйте ссылку предоставленную на их сайте;
-
Читайте отзывы и рейтинги. Поддельные приложения зачастую имеют много плохих отзывов от жертв мошенничества, поэтому обязательно проверяйте это перед установкой. Тем не менее, вы также должны скептически относиться к приложениям, у которых исключительно положительные оценки и комментарии. Любое легальное приложение имеет свою долю отрицательных отзывов;
-
Проверьте информацию о разработчике приложения, компании, адрес электронной почты и веб-сайт. Вы должны убедиться во всей предоставленной информации, а также в том, что приложение действительно связано с биржей;
-
Проверьте количество загрузок, это также следует учитывать. Маловероятно, что популярное мобильное приложение крипто-биржи будет иметь небольшое количество скачиваний;
-
Активируйте 2FA в своем аккаунте. Хотя это не защитит вашу учетную запись на все 100%, но мошенникам будет намного сложнее получить к ней доступ и это существенно может помочь защитить ваши средства, даже если вы станете жертвой фишинга.
Крипто-кошельки
Существует множество различных поддельных приложений. Суть одного из видов заключается в получении личной информации от пользователей, такой как пароли от кошельков и приватные ключи.
В некоторых случаях такие приложения предоставляют ранее сгенерированные публичные адреса и они предполагают, что пользователи могут внести на них депозит. Однако в свою очередь они не получают доступ к приватным ключам и следовательно не владеют средствам, которые отправляли.
Такие поддельные кошельки были созданы исключительно для наиболее популярных криптовалют, таких как Ethereum, Neo и к сожалению многие пользователи стали жертвами этого.
Меры предосторожности, которые следует предпринять, чтобы не стать жертвой:
-
Вышеперечисленные операции с приложениями для доступа к бирже в равной степени актуальны. Однако при работе с кошельками вам обязательно следует учитывать, что при первом запуске вы должны получить новый публичный адрес и приватный ключ (или мнемонические фразы). Настоящее приложение-кошелек позволяет экспортировать приватные ключи, но также следует убедиться в том, что генерация новых пар ключей не была скомпрометирована. Поэтому вы должны использовать программное обеспечение с отличной репутацией (желательно с открытым исходным кодом);
-
Даже если приложение предоставляет вам приватный ключ (или мнемонические фразы), вы должны убедиться в том, что с его помощью вы можете получить доступ к своему кошельку. Например, некоторые биткойн-кошельки позволяют пользователям импортировать свои приватные ключи или фразы для визуализации адресов и доступа к средствам. Чтобы минимизировать риск компрометации ключей и фраз, вы можете выполнить это на компьютере с воздушным зазором (без доступа к интернету).
Криптоджекинг
Криптоджекинг был ярким фаворитом среди киберпреступлений из-за низкого барьера для входа и накладных расходов. Кроме того он предполагает долгосрочный повторяющийся доход. Несмотря на более низкую вычислительную мощность по сравнению с ПК, мобильные устройства все чаще становятся жертвами этой атаки.
Помимо криптоджекинга с использованием веб-браузера, киберпреступники также разрабатывают программы, которые имеют вид обычных игровых, служебных или образовательных приложения. Однако многие из них предназначены для скрытого майнинга криптовалюты в фоновом режиме.
Также существуют приложения, которые рекламируются как легитимный майнинг для вашего устройства, но по факту награду получает разработчик, а не пользователь. Что еще хуже, киберпреступники становятся все более изощренными, разрабатывая более несущественные алгоритмы майнинга, чтобы избежать обнаружения.
Криптоджекинг невероятно опасен для ваших мобильных устройств, поскольку он ухудшает производительность и ускоряет износ процессора и батареи. Хуже того, он может выступать в роли троянской программы в дополнение к другим вирусам.
Следующие шаги которые следует предпринять чтобы защитить себя:
-
Загружайте приложения только из официальных источников, таких как Google Play. Пиратские программы предварительно не проверяются и скорее всего содержат скрипт с криптоджекингом;
-
Отслеживайте работу своего телефона в случае быстрого разряда батареи или перегрева. При выявлении причины завершите работу приложений, которые это вызывают;
-
Обновляйте свой девайс и приложения, чтобы исправить уязвимости прошлых версий прошивки;
-
Используйте веб-браузер, который защитит вас от криптоджекинга или установите специальные расширения такие как: MinerBlock, NoCoin и Adblock;
-
Если это возможно, установите антивирус на ваш смартфон и регулярно обновляйте его.
Free giveaway и фальшивые приложения для майнинга
Некоторые из программ, которые “занимаются майнингом криптовалюты” для своих пользователей, по факту ничего не делают, кроме демонстрации рекламных объявлений. Они стимулируют держать приложения открытыми, отражая увеличение вознаграждений с течением времени. Некоторые программы принуждают пользователей оставлять максимальную оценку, чтобы получить награду. В конечном счете ни одна из этих платформ не занималась майнингом и их пользователи не получат свое вознаграждение.
Чтобы защититься от такого мошенничества следует понимать, что для большинства криптовалюты майнинг требует высокоспециализированного оборудования (ASIC), а это означает, что невозможно майнить на мобильном устройстве. Какие бы суммы вы там не добыли, они ничего не значат. Держитесь подальше от подобных приложений.
Клипер
Это программы которые изменяют адрес, который вы копируете и заменяют его на другой. Таким образом, жертва хоть и может скопировать правильный адрес получателя для обработки транзакции, тот в свою очередь заменяется адресом злоумышленника.
Чтобы не стать жертвой таких приложений, вот некоторые из мер предосторожности, которые следует учитывать при отправке транзакций:
-
Всегда дважды, а лучше трижды проверьте адрес, который вы вставляете в поле получателя. Все операции в блокчейне необратимы, поэтому вы всегда должны быть осторожны.
-
Лучше всего проверить весь адрес, а не только его части. Некоторые приложения настолько умны, что используют адреса, которые очень похожи на ваш адрес получателя.
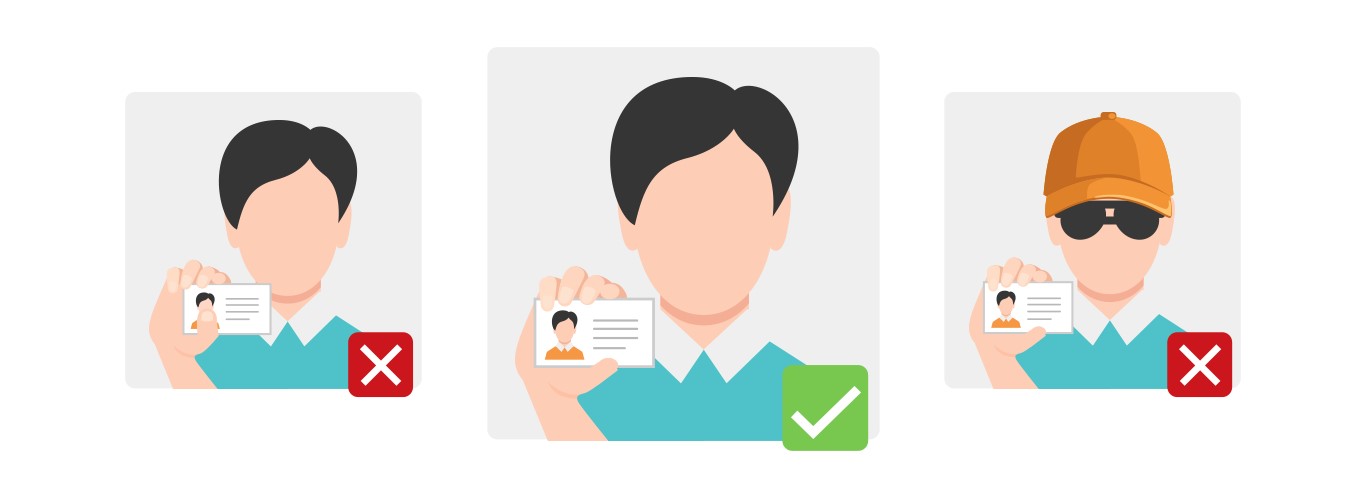
Подмена SIM-карты
При мошенничестве с подменой SIM-карт злоумышленник получает доступ к номеру телефона пользователя используя различные методы социальной инженерии, чтобы обмануть операторов мобильной связи в целях получения новой SIM-карты. Самым известным случаем подобной махинации стал криптовалютный предприниматель Майкл Терпин. Он утверждал, что AT&T небрежно относятся к учетным данным его мобильного телефона, в результате чего он потерял токенов на сумму более 20 млн. долларов США.
После того, как киберпреступник получил доступ к вашему номеру, он может использовать его для обхода любого 2FA, который с ним связан, после чего он получает доступ к вашим кошелькам и аккаунтам на биржах.
Еще один метод, который могут использовать киберпреступники, это отслеживать ваши SMS-сообщения. Недостатки телекоммуникационных сетей позволяют злоумышленникам перехватить ваши сообщения, которые включают в себя элемент второго фактора аутентификации.
Особую обеспокоенность этой атаки вызывает то, что пользователи не обязаны предпринимать какие-либо действия, такие как загрузка поддельного программного обеспечения или переход по зараженной ссылке.
Меры предосторожности, которые необходимо соблюдать, чтобы не стать жертвой такого мошенничества:
-
Не используйте свой основной мобильный номер для SMS 2FA. Вместо этого пользуйтесь приложениями наподобии Google Authenticator или Authy, чтобы защитить свой аккаунт. В таком случае киберпреступники не получат доступ к информации даже если у них будет ваш номер телефона. Кроме того вы можете использовать аппаратный 2FA, с помощью YubiKey или Google Titan;
-
Не разглашайте вашу идентификационную информацию в социальных сетях, например номер вашего мобильного телефона. Эта информация может быть использована против вас;
-
Не объявляйте в социальных сетях о том, что у вас есть криптовалюта, так как это сразу сделает вас целью, если вы уже находитесь в таком положении, избегайте разглашения остальной личной информации, а также биржи и кошельки которые вы используете;
-
Договоритесь с провайдером мобильной связи о защите вашего мобильного номера. Это может означать наличие пин-кода или пароля с указанием на то, что только те кто знают его могут вносить изменения в ваш персональный аккаунт. Помимо этого вы можете договориться о том, что изменения должны происходить исключительно при вашем личном присутствии.
WiFi
Киберпреступники постоянно ищут слабые места в ваших мобильных девайсах, особенно если они связаны с криптовалютой. Одним из таких слабых мест является доступ к интернету с помощью WiFi. Общественные точки доступа к интернету небезопасны и пользуясь ими вы не должны пренебрегать мерами предосторожности прежде чем подключиться, в противном случае вы рискуете предоставить доступ к данным вашего устройства. Все действия связанные с обеспечением вашей безопасности мы рассмотрели в статье об общественном WiFi.
Заключение
Мобильные телефоны стали неотъемлемой частью нашей жизни и по факту они настолько связаны с цифровой идентификацией, что могут стать вашим слабым местом. Киберпреступники знают об этом и будут продолжать искать способы использовать это. Защита ваших мобильных устройств больше не является обязательной, так как это стало необходимостью, поэтому всегда будьте начеку и оставайтесь в безопасности.